| Digital List Price: | $110.39 |
| Kindle Price: | $77.23 Save $33.16 (30%) |
| Sold by: | Amazon.com Services LLC |
Your Memberships & Subscriptions
Download the free Kindle app and start reading Kindle books instantly on your smartphone, tablet, or computer - no Kindle device required.
Read instantly on your browser with Kindle for Web.
Using your mobile phone camera - scan the code below and download the Kindle app.
OK
Computer Security: Art and Science 2nd Edition, Kindle Edition
The Comprehensive Guide to Computer Security, Extensively Revised with Newer Technologies, Methods, Ideas, and Examples
In this updated guide, University of California at Davis Computer Security Laboratory co-director Matt Bishop offers clear, rigorous, and thorough coverage of modern computer security. Reflecting dramatic growth in the quantity, complexity, and consequences of security incidents, Computer Security, Second Edition, links core principles with technologies, methodologies, and ideas that have emerged since the first edition’s publication.
Writing for advanced undergraduates, graduate students, and IT professionals, Bishop covers foundational issues, policies, cryptography, systems design, assurance, and much more. He thoroughly addresses malware, vulnerability analysis, auditing, intrusion detection, and best-practice responses to attacks. In addition to new examples throughout, Bishop presents entirely new chapters on availability policy models and attack analysis.
- Understand computer security goals, problems, and challenges, and the deep links between theory and practice
- Learn how computer scientists seek to prove whether systems are secure
- Define security policies for confidentiality, integrity, availability, and more
- Analyze policies to reflect core questions of trust, and use them to constrain operations and change
- Implement cryptography as one component of a wider computer and network security strategy
- Use system-oriented techniques to establish effective security mechanisms, defining who can act and what they can do
- Set appropriate security goals for a system or product, and ascertain how well it meets them
- Recognize program flaws and malicious logic, and detect attackers seeking to exploit them
This is both a comprehensive text, explaining the most fundamental and pervasive aspects of the field, and a detailed reference. It will help you align security concepts with realistic policies, successfully implement your policies, and thoughtfully manage the trade-offs that inevitably arise.
Register your book for convenient access to downloads, updates, and/or corrections as they become available. See inside book for details.
- ISBN-13978-0321712332
- Edition2nd
- PublisherAddison-Wesley Professional
- Publication dateNovember 27, 2018
- LanguageEnglish
- File size17491 KB
Customers who bought this item also bought
Editorial Reviews
About the Author
Matt Bishop is a professor in the Department of Computer Science at the University of California at Davis. His main research interest is the analysis of vulnerabilities in computer systems, including modeling them, building tools to detect vulnerabilities, and ameliorating or eliminating them. He works in the areas of network security, including the study of denial of service attacks and defenses, policy modeling, software assurance testing, resilience, and formal modeling of access control. He was co-chair of the Joint Task Force that developed the Cybersecurity Curricula 2017: Curriculum Guidelines for Post-Secondary Degree Programs in Cybersecurity, released in December 2017. He earned his Ph.D. in computer science from Purdue University in 1984.
Product details
- ASIN : B07KXYK9XH
- Publisher : Addison-Wesley Professional; 2nd edition (November 27, 2018)
- Publication date : November 27, 2018
- Language : English
- File size : 17491 KB
- Simultaneous device usage : Up to 5 simultaneous devices, per publisher limits
- Text-to-Speech : Enabled
- Enhanced typesetting : Enabled
- X-Ray : Not Enabled
- Word Wise : Not Enabled
- Sticky notes : Not Enabled
- Print length : 2766 pages
- Best Sellers Rank: #1,371,008 in Kindle Store (See Top 100 in Kindle Store)
- #521 in Network Security (Kindle Store)
- #1,397 in Computer Hacking
- #1,578 in Computer Network Security
- Customer Reviews:
About the author

Matt Bishop received his Ph.D. in computer science from Purdue University, where he specialized in computer security, in 1984. He was a research scientist at the Research Institute of Advanced Computer Science and was on the faculty at Dartmouth College before joining the Department of Computer Science at the University of California at Davis.
His main research area is the analysis of vulnerabilities in computer systems, including modeling them, building tools to detect vulnerabilities, and ameliorating or eliminating them. This includes detecting and handling all types of malicious logic. He is active in the areas of network security, the study of denial of service attacks and defenses, policy modeling, software assurance testing, and formal modeling of access control. He also studies the issue of trust as an underpinning for security policies, procedures, and mechanisms.
He has examined electronic voting systems and they way in which they are used. He was a co-Principal Investigator for the California Top-to-Bottom Review of certified systems used in California, and also participated in several other reviews of e-voting systems.
He is active in information assurance education, is a charter member of the Colloquium on Information Systems Security Education, and led a project to gather and make available many unpublished seminal works in computer security. His textbook, Computer Security: Art and Science, was published in December 2002 by Addison-Wesley Professional, and another one, Introduction to Computer Security, in 2005.
He also teaches software engineering, machine architecture, operating systems, programming, and (of course) computer security.
Customer reviews
Customer Reviews, including Product Star Ratings help customers to learn more about the product and decide whether it is the right product for them.
To calculate the overall star rating and percentage breakdown by star, we don’t use a simple average. Instead, our system considers things like how recent a review is and if the reviewer bought the item on Amazon. It also analyzed reviews to verify trustworthiness.
Learn more how customers reviews work on AmazonReviews with images
-
Top reviews
Top reviews from the United States
There was a problem filtering reviews right now. Please try again later.
Since the 2nd ed. launched in Nov 2018 (mod the publisher blurb and 2-3 lines reviews on Amazon) no one has written a more i- depth review, in part because it’s not for beginners (neither students, nor teachers).
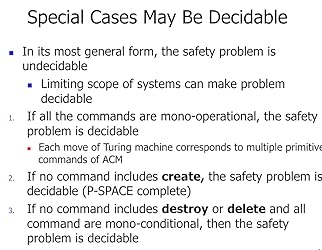
You need a pedagogically experienced subject matter expert with memory spanning decades to make the material come alive and relevant to today’s environment. This requires grasping complex theory and conveying why said theory is relevant today, then mapping it to practical modern real-life issues and systems such as blockchain, ledgers, CD/CI, SaaS, FaaS, CDN infrastructure (google APNIC Huston “Death of Transit"). The putative pedagogue must be willing and able to explain the link between HRU and undecidability viz the so-called ‘safety problem’ (see screenshots; this security version of the halting problem - can you reach an insecure state? ) which directly impacts language design (google “JPL C coding” to get a feeling for the C of NASA’s flight software expressly reduced to allow for safety guarantees) which in turn affects the security yield of static source code analysis techniques on such code bases. There are many more such links to be expounded upon.
Another deep passage is given in Sec. 4.8 trust assumption (see screenshot) :
"Trust underlies all policies and enforcement mechanisms. [..] Understanding the assumptions and the trust involved in any policies and mechanisms deepens one’s understanding of the security of a system."
Spectre and Rowhammer vectors are likely the most prominent recent examples of deepening our understanding of the security of a hardware system (see screenshot and google "Mcilroy Verwaest 2019 Spectre is here to stay").
Why weren’t these vulnerabilities identified and remedied decades ago? The answer is that horribile dictu vulnerabilities are created by dynamics in adversarial environments, rather than inherent feature of systems, as heretical as this may sound. Spectre thus illustrates what happens when specific assumptions are violated; in this case the assumption of a hardware threat model scoped to random errors (ie Nature is cruel - stray neutrinos perhaps - but not malicious) had to make way to a hardware threat model including non-random, intelligent adaptive adversaries.
Adversarial dynamics can create brand new attack surfaces, emphasizing the need to understand "the assumptions and the trust involved in any policies and mechanisms", as Bishop stated in Sec. 4.8. Google "CTF solution ret2 systems "Hotel California" Intel TSX jail challenge" to see another example of a novel CPU bug discovery as unintended consequence of a CTF challenge.
Part III discusses Policy at length, among them classic seemingly old-fashioned models such as the Bell-LaPadula model for Confidentiality and the Biba low watermark Integrity model. Grokking these models and their characteristics is crucial to understanding why eg the AWS S3 access control model is broken (google "An API Worm In The Making: Thousands Of Secrets Found In Open S3 Buckets") and one needs professional assistance to set the S3 access control permission properly (google "Zelkova: AWS automated SMT reasoning on resource policies").
Parts of the book seem not to have been updated in twenty years (eg many ftp, rsh illustrations). In my opinion, this is a valid but quite minor critique since those examples remain valid for the one-off concepts Bishop needs to illustrate. Some of the most interesting tidbits are buried in the research issues (eg Sec. 9.8).
Summa summarum: This hefty work (1440+ pages, 2250+ references) can be made to shine, but it will not be easy. The publisher's stated target audience - junior / senior undergraduates – is in my professional opinion wildly and impossibly optimistic. Even at first rate institutions it will be a very hard sell on account of the sometimes-excruciating plain dryness of the material. It took me as a motivated PhD SME 4 weeks of 6 hours of work per day, 4 days a week working through and warming to the 1st edition 17 years ago.
I endeavored to make a short case for Bishop's immense value. Any failing in this regard is mine alone and not the author’s. If push came to shove as a computer security pedagogue and professional, you would need three books; this one by Bishop, Anderson's "Security Engineering" and Ericksson's "Hacking: The Art of Exploitation". The rest is, as they say, commentary.
Daniel Bilar, Norwich University, Northfield VT.
Reviewed in the United States on May 10, 2021
Since the 2nd ed. launched in Nov 2018 (mod the publisher blurb and 2-3 lines reviews on Amazon) no one has written a more i- depth review, in part because it’s not for beginners (neither students, nor teachers).
You need a pedagogically experienced subject matter expert with memory spanning decades to make the material come alive and relevant to today’s environment. This requires grasping complex theory and conveying why said theory is relevant today, then mapping it to practical modern real-life issues and systems such as blockchain, ledgers, CD/CI, SaaS, FaaS, CDN infrastructure (google APNIC Huston “Death of Transit"). The putative pedagogue must be willing and able to explain the link between HRU and undecidability viz the so-called ‘safety problem’ (see screenshots; this security version of the halting problem - can you reach an insecure state? ) which directly impacts language design (google “JPL C coding” to get a feeling for the C of NASA’s flight software expressly reduced to allow for safety guarantees) which in turn affects the security yield of static source code analysis techniques on such code bases. There are many more such links to be expounded upon.
Another deep passage is given in Sec. 4.8 trust assumption (see screenshot) :
"Trust underlies all policies and enforcement mechanisms. [..] Understanding the assumptions and the trust involved in any policies and mechanisms deepens one’s understanding of the security of a system."
Spectre and Rowhammer vectors are likely the most prominent recent examples of deepening our understanding of the security of a hardware system (see screenshot and google "Mcilroy Verwaest 2019 Spectre is here to stay").
Why weren’t these vulnerabilities identified and remedied decades ago? The answer is that horribile dictu vulnerabilities are created by dynamics in adversarial environments, rather than inherent feature of systems, as heretical as this may sound. Spectre thus illustrates what happens when specific assumptions are violated; in this case the assumption of a hardware threat model scoped to random errors (ie Nature is cruel - stray neutrinos perhaps - but not malicious) had to make way to a hardware threat model including non-random, intelligent adaptive adversaries.
Adversarial dynamics can create brand new attack surfaces, emphasizing the need to understand "the assumptions and the trust involved in any policies and mechanisms", as Bishop stated in Sec. 4.8. Google "CTF solution ret2 systems "Hotel California" Intel TSX jail challenge" to see another example of a novel CPU bug discovery as unintended consequence of a CTF challenge.
Part III discusses Policy at length, among them classic seemingly old-fashioned models such as the Bell-LaPadula model for Confidentiality and the Biba low watermark Integrity model. Grokking these models and their characteristics is crucial to understanding why eg the AWS S3 access control model is broken (google "An API Worm In The Making: Thousands Of Secrets Found In Open S3 Buckets") and one needs professional assistance to set the S3 access control permission properly (google "Zelkova: AWS automated SMT reasoning on resource policies").
Parts of the book seem not to have been updated in twenty years (eg many ftp, rsh illustrations). In my opinion, this is a valid but quite minor critique since those examples remain valid for the one-off concepts Bishop needs to illustrate. Some of the most interesting tidbits are buried in the research issues (eg Sec. 9.8).
Summa summarum: This hefty work (1440+ pages, 2250+ references) can be made to shine, but it will not be easy. The publisher's stated target audience - junior / senior undergraduates – is in my professional opinion wildly and impossibly optimistic. Even at first rate institutions it will be a very hard sell on account of the sometimes-excruciating plain dryness of the material. It took me as a motivated PhD SME 4 weeks of 6 hours of work per day, 4 days a week working through and warming to the 1st edition 17 years ago.
I endeavored to make a short case for Bishop's immense value. Any failing in this regard is mine alone and not the author’s. If push came to shove as a computer security pedagogue and professional, you would need three books; this one by Bishop, Anderson's "Security Engineering" and Ericksson's "Hacking: The Art of Exploitation". The rest is, as they say, commentary.
Daniel Bilar, Norwich University, Northfield VT.






The material is interesting and compellingly presented. There is information both at practical and theoretical levels.
However, the teaching tracks through the book are not linear -- for instance the recommended path through the book for undergraduates is chapters 1, 10, 11, part of 2 and most of 4, parts of 5,6,7,8, all of 14, and so on. For a first-time user of the book, this makes lecture preparation more difficult than one would hope for.
In any case, it's an excellent book and it has enough depth to make it a great investment for students seriously interested in InfoSec. It's also very workable (as much as any textbook, anyway) in Kindle form.